OpenAI Mixpanel Incident: On November 9, 2025, OpenAI disclosed a security incident — but not inside their own systems.The issue originated from Mixpanel, one of
Tag: HackerVault
OWASP Security Misconfiguration – 7 Critical Risks & How to Fix Them
OWASP security misconfiguration is one of the most common and dangerous vulnerabilities in modern applications. It appears in the OWASP Top 10 because misconfigured systems,
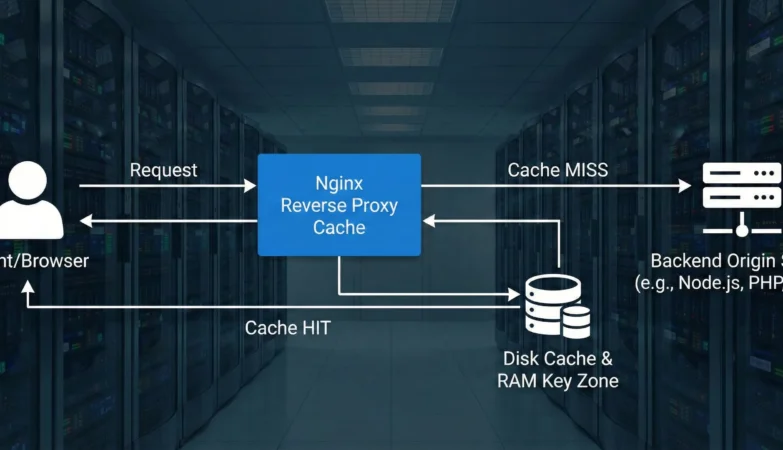
Nginx Reverse Proxy Guide – 5 Powerful Steps
Nginx reverse proxy guide — this feature is one of the most powerful ways to secure, optimize, and scale modern web applications. By placing Nginx
Nginx Explained: Reverse Proxy, Forward Proxy, WAF, ModSecurity & Full Functionality Guide
🔍 Introduction Nginx (engine-x) is a fast, flexible web server and proxy used for reverse proxying, SSL termination, load balancing, caching, and WAF integration. This
OWASP Top 10 2025: What’s New, Changed & Security Guide
🔍 Introduction Every few years, OWASP publishes the Top 10 list — the world’s most trusted benchmark of web-application security risks.The 2025 Release Candidate (RC1)
How Does JA4/JA4H Analyze Client Architecture for WAF Detection?
Client Architecture in JA4/JA4H WAF Detection plays a crucial role in understanding the true nature of the device connecting to your web applications. JA4 and
Charon Ransomware Strikes Middle East: A New Era of APT-Level Ransomware Attacks
In August 2025, the Charon ransomware attack has been detected targeting critical sectors across the Middle East, marking a new phase of sophisticated ransomware blending
TLS Handshake in Secure Communication: How It Protects the Internet
Transport Layer Security (TLS) stands as a cornerstone of modern internet security, a protocol meticulously designed to ensure privacy and data integrity across digital communications.
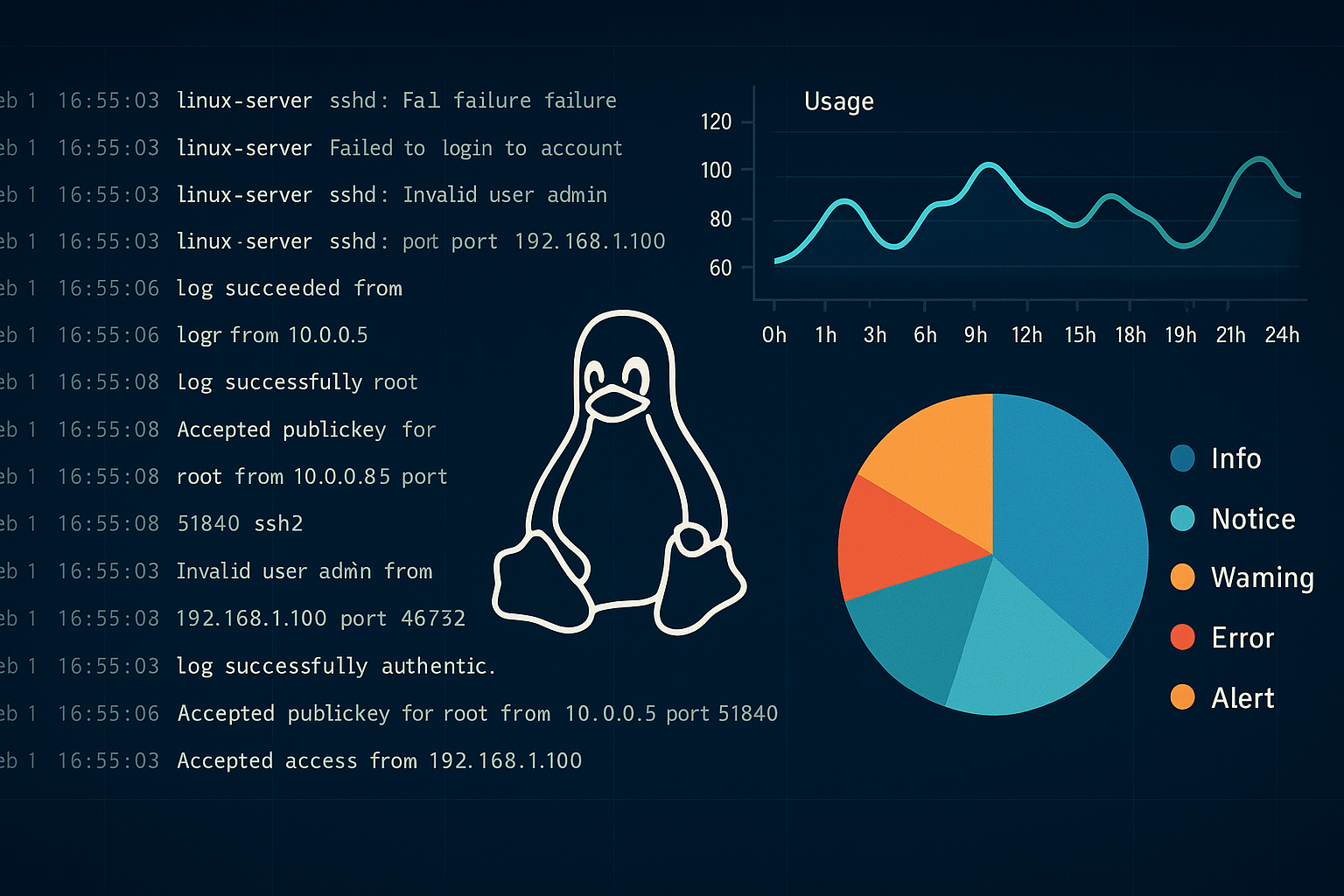
Mastering Linux Log Monitoring for SOC: A Powerful Guide to Security & Compliance
Linux log monitoring for SOC teams is a critical practice in modern cybersecurity. Think of your Linux servers as tireless digital detectives — constantly capturing
Azure Elasticsearch Service Comparison: Azure AI Search vs Fabric vs ADX
Managing vast datasets often demands capabilities similar to Elasticsearch for robust search and real-time analytics. If your infrastructure is primarily on Azure, you’ll want managed