Web Application Firewalls (WAFs) are now a core part of modern web security architecture, sitting at the HTTP edge to detect and block attacks before
Category: Cybersecurity Tutorials
Step-by-step tutorials for learning cybersecurity concepts and hands-on skills.
CVE-2025-55182: 7 Critical Insights Into the React Server Components RCE
CVE-2025-55182 is a critical pre-authentication remote code execution (RCE) vulnerability in React Server Components (RSC), impacting production deployments of React 19 that rely on Server
7 Powerful OWASP Authentication Failures
OWASP Authentication Failures remain the leading cause of breaches across web apps, mobile apps, APIs, cloud systems, and microservices. This extended edition (3000+ words) covers
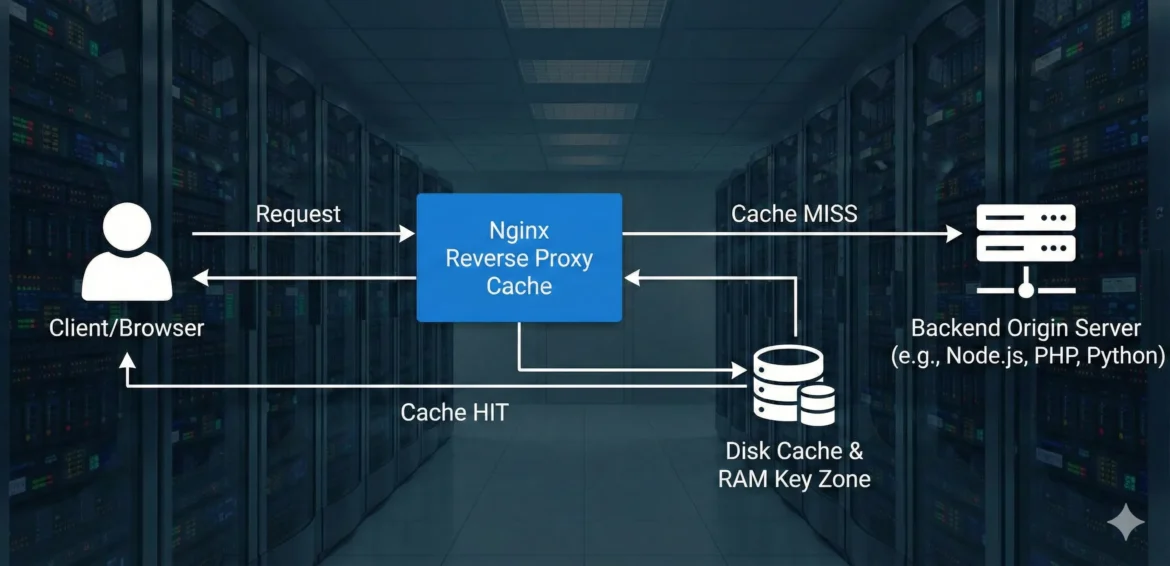
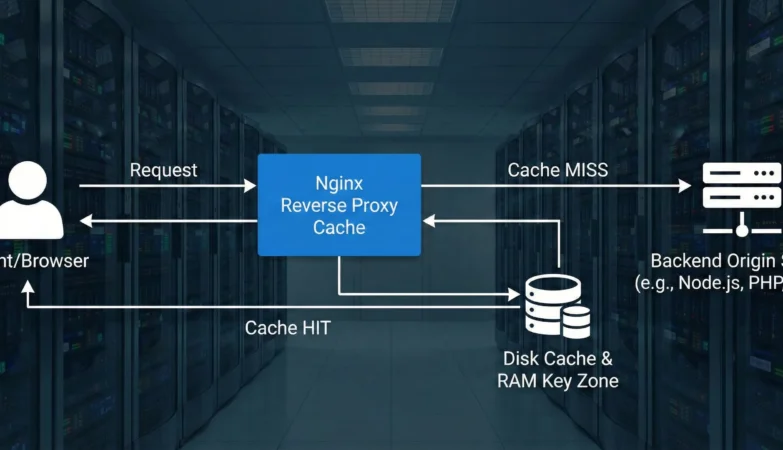
5 Powerful Nginx Caching Secrets to Drastically Boost Performance
The path to a HackerVault-grade fast and resilient web application infrastructure inevitably leads through efficient caching. And when we talk about high-performance web serving, Nginx
7 Powerful Ways to Prevent Cryptographic Failures
Cryptographic failures remain one of the most critical risks in modern security systems. In fact, the exact focus keyword cryptographic failures appears as the second
OWASP Security Misconfiguration – 7 Critical Risks & How to Fix Them
OWASP security misconfiguration is one of the most common and dangerous vulnerabilities in modern applications. It appears in the OWASP Top 10 because misconfigured systems,
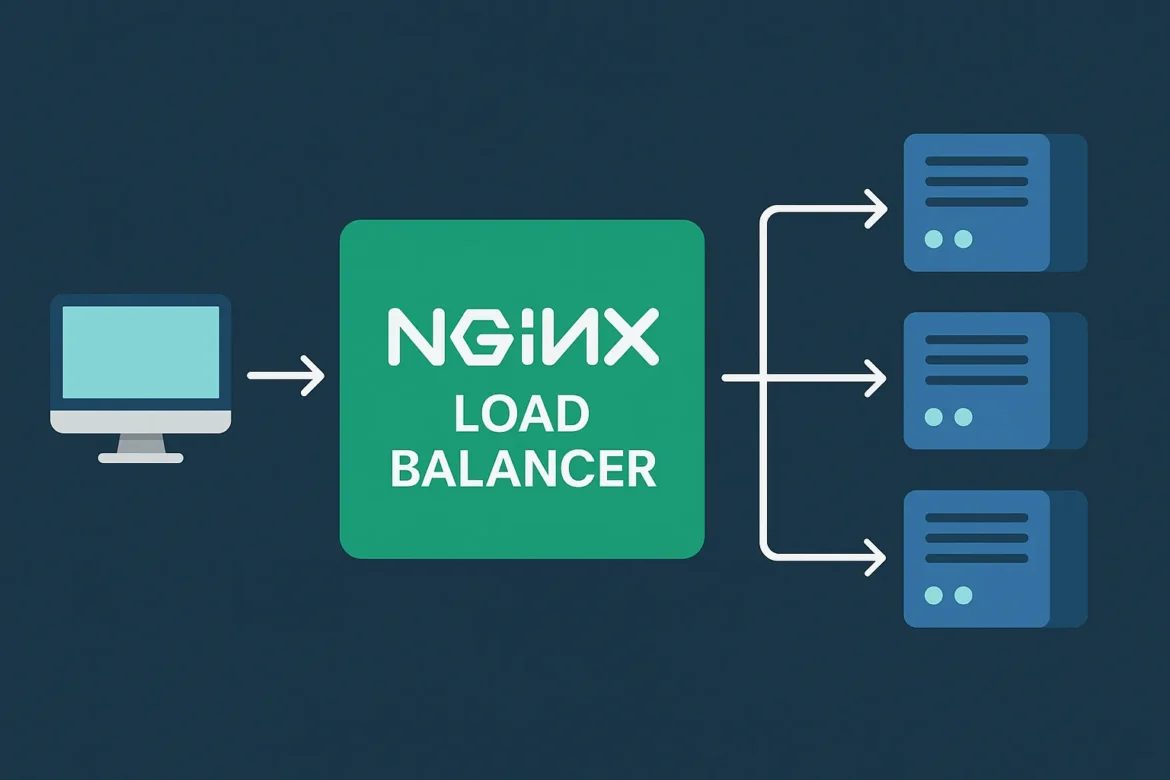
Nginx Load Balancer Guide – 5 Powerful Techniques to Boost Speed, Reliability & Security
Nginx load balancer is one of the most important components in modern web infrastructure. As applications scale across microservices, containers, and multi-node backends, Nginx remains
OWASP Top 10 2025: What’s New, Changed & Security Guide
🔍 Introduction Every few years, OWASP publishes the Top 10 list — the world’s most trusted benchmark of web-application security risks.The 2025 Release Candidate (RC1)
How Does JA4/JA4H Analyze Client Architecture for WAF Detection?
Client Architecture in JA4/JA4H WAF Detection plays a crucial role in understanding the true nature of the device connecting to your web applications. JA4 and
TLS Handshake in Secure Communication: How It Protects the Internet
Transport Layer Security (TLS) stands as a cornerstone of modern internet security, a protocol meticulously designed to ensure privacy and data integrity across digital communications.