🔐 Introduction Ransomware attacks have grown from small-time scams to organized cybercrime operations. In 2024, they cost organizations billions and continue to evolve with new

Recent Posts
The Double-Edged Sword of Automation: A Deep Dive into ACME and the Recent Cloudflare Zero-Day
Date: January 21, 2026, Tags: #CyberSecurity #Cloudflare #ACME #SSL #ZeroDay #DevOps In the last decade,…
Seclang Deep Dive: Building Smart WAF Rules with Coraza and ModSecurity
Web Application Firewalls (WAFs) are now a core part of modern web security architecture, sitting…
CVE-2025-55182: 7 Critical Insights Into the React Server Components RCE
CVE-2025-55182 is a critical pre-authentication remote code execution (RCE) vulnerability in React Server Components (RSC),…
7 Powerful OWASP Authentication Failures
OWASP Authentication Failures remain the leading cause of breaches across web apps, mobile apps, APIs,…
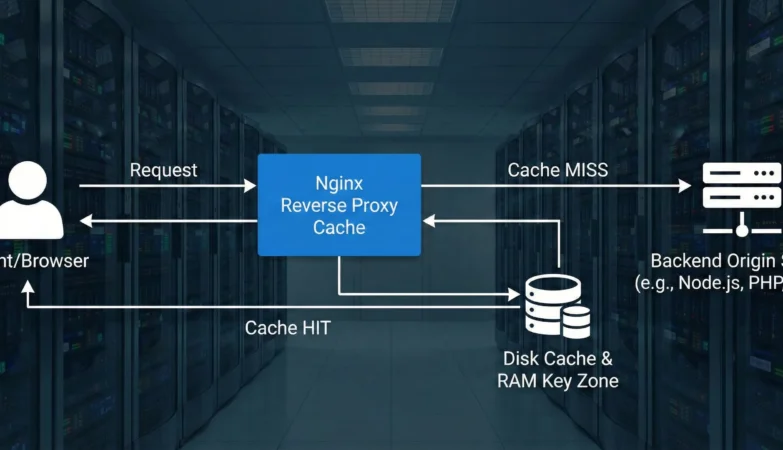
5 Powerful Nginx Caching Secrets to Drastically Boost Performance
The path to a HackerVault-grade fast and resilient web application infrastructure inevitably leads through efficient…
7 Powerful Ways to Prevent Cryptographic Failures
Cryptographic failures remain one of the most critical risks in modern security systems. In fact,…